Здравейте, от известно време изследвам една тема, а именно как да си направим телефонна централа за дома и малкия офис.
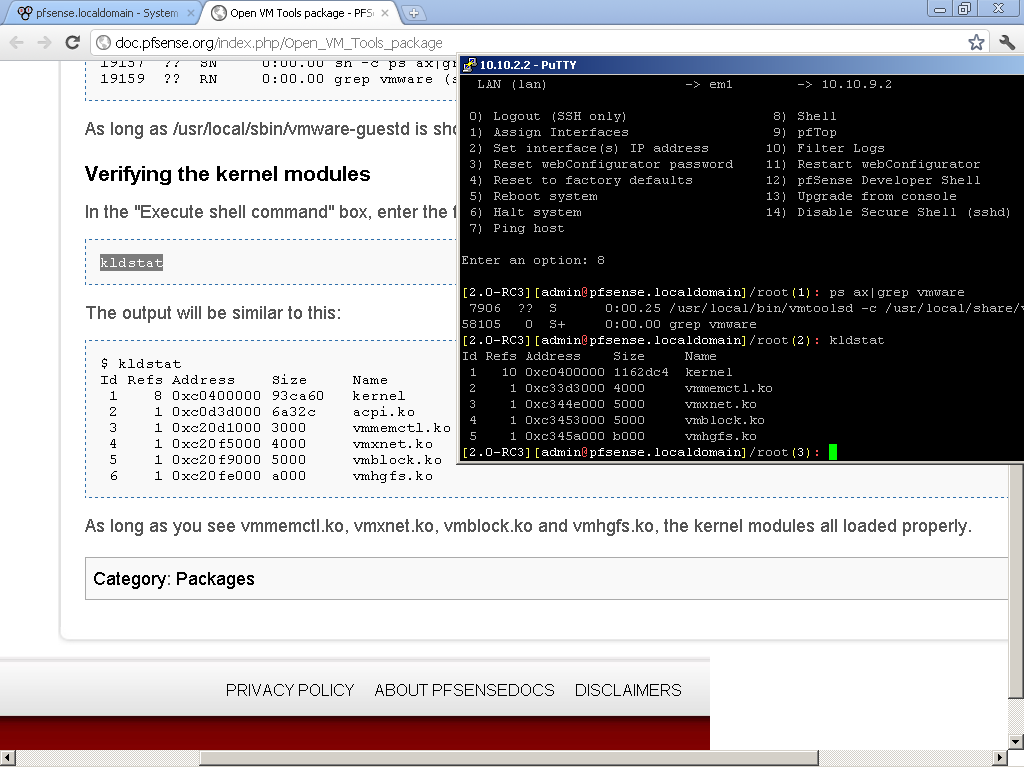
Първо си поиграх със Asterisk 1.4/1.6 на виртуална машина със soft phones.
Имах желание да изпробвам и с hard phones, въпроса беше коя марка и модел да избера. Тук на помощ дойде един от най – добрите сайтове, поне според мен за информация относно VoIP http://www.voip-info.org/. След продължително търсене на подходящи телефони съвместими с Asterisk, избрах Linksys SPA 941. Избрах го защото, не са ми необходими цветен екран, видеокамера, power over Ethernet, wireless и повече от 1, 2 линии.

Тук може да видите повече информация за него: http://www.voip-info.org/wiki/view/SPA-941
За да добиете представа какви алтернативи има вижте новата гама на Cisco, тук има едно прилично ревю:
http://www.asterisktutorials.com/first-look-at-the-cisco-spa500-phones/
В един момент ми попадна брошура на JAR, и какво да видя в нея SPA 921/941 на доста приятни цени. Не се сдържах и си взех два. Все още са в каталога им като цената на 941 вече е 200 лева.
С помощ на този видео tutorial ги свързах с Asterisk-a за 10 минути.
http://www.asterisktutorials.com/linksys-spa941942-sip-phones/
Впоследствие ги flash-нах до последната версия на firmware-a, която в момента е 5.1.8. Става лесно и и бързо.
http://www.cisco.com/en/US/products/ps10038/index.html
От няколко години използвам OpenWRT и DD-WRT чудесни дистрибуции побираща се на безжични рутери. И двете предлагат уникални функции които са недостъпни от stock firmware-a на който и да е безжичен рутер.
На един етап започнаха да се появяват версии включващи и Asterisk. Реших да пробвам как ще се държи ако сложа и телефонната централа на устройство. Като се има предвид ползите от такава играчка, без движещи се части, без шум и ниска консумация на електричество.
Разбира се тук е момента да спомена че е добре да се провери за съвместимост на модела със въпросната дистрибуция.
Ето тук за DD-WRT:
http://www.dd-wrt.com/wiki/index.php/Supported_Devices
и тук за OpenWRT
http://wiki.openwrt.org/toh/start
Като се замисля последните няколко безжични рутери които са ми попадали в ръцете не са издържали повече от 5 минути със stock firmware.
Като критерии за оценка на устройство може да се вземе Flash Memory. Това е памет на която се инсталира операционната система. Тоест ако имате 4 MB не можете да сложите такава която изисква 8 MB, примерно. Правилото на Мечо Пух “Колкото повече, Толкова Повече” тук е валидно с пълна сила. Поради факта че ползвам големите build-ове на dd-wrt изискващи поне 8 MB си харесах Asus RT-N16. Той е със 128MB RAM, 32 MB Flash Memory, a процесор му е на 480 MHz. Освен това има 2 USB 2.0 порта на които може да включи флашка, външен диск или принтер.

Незнам защо но този модел не се предлагаше в България доста време, въпреки че е излязъл още преди една – две години. Както и да е, от преди месец – два се предлага в Мост. Цената му е около 270 лева.
Последния hardware който ми беше необходим е един USB Flash Drive, или както ги наричаме флаш-ки. На него сложих Optware, за повече информация : http://en.wikipedia.org/wiki/Optware
Не можах да си намеря PQI Cool Drive U338 Pro която има доста прилични скорости и се задоволих с една PQI Cool Drive U339H, Titanium 4 GB за около 25 лева. Забелязвате ли как вече не пишат скоростите на read/write на флашките?
И така да видим разходите до тук:
Asus RT-N16 – 270 лв.
Linksys SPA 941 x2 – 350 лв.
PQI U339H, Titanium 4GB – 25 лв.
Общо: 645 лв.
Преди да пристъпя към инсталация и конфигурация прочетох тази тема във форума:
http://www.dd-wrt.com/phpBB2/viewtopic.php?t=43787&postdays=0&postorder=asc&start=0
GUI-то описано там не сработи и за мен, за това реших да рискувам с asterisk-gui, вместо него.
Да преминем към инсталацията:
Свалих последната налична версия от www.dd-wrt.com: dd-wrt.v24-14471_NEWD-2_K2.6_big.bin, вече има по – нови.
След това следвах този guide за да инсталирам и Optware:
http://www.dd-wrt.com/wiki/index.php/Optware%2C_the_Right_Way
и вече имам и този пакет
asterisk14 – 1.4.22.1-1 – Asterisk is an Open Source PBX and telephony toolkit.
След което добавих всички пакети със звуци използвайки ipkg-opt:
asterisk14-core-sounds-en-alaw – 1.4.8-1 – asterisk-core-sounds-en-alaw
asterisk14-core-sounds-en-g729 – 1.4.8-1 – asterisk-core-sounds-en-g729
asterisk14-core-sounds-en-gsm – 1.4.8-1 – asterisk-core-sounds-en-gsm
asterisk14-core-sounds-en-ulaw – 1.4.8-1 – asterisk-core-sounds-en-ulaw
asterisk14-extra-sounds-en-alaw – 1.4.7-1 – asterisk-extra-sounds-en-alaw
asterisk14-extra-sounds-en-g729 – 1.4.7-1 – asterisk-extra-sounds-en-g729
asterisk14-extra-sounds-en-gsm – 1.4.7-1 – asterisk-extra-sounds-en-gsm
asterisk14-extra-sounds-en-ulaw – 1.4.7-1 – asterisk-extra-sounds-en-ulaw
asterisk14-moh-freeplay-alaw – 0.0.0-1 – asterisk-moh-freeplay-alaw
asterisk14-moh-freeplay-g729 – 0.0.0-1 – asterisk-moh-freeplay-g729
asterisk14-moh-freeplay-gsm – 0.0.0-1 – asterisk-moh-freeplay-gsm
asterisk14-moh-freeplay-ulaw – 0.0.0-1 – asterisk-moh-freeplay-ulaw
и накрая добавих и GUI-то:
asterisk-gui – 2.0svn-r4045-1 – Asterisk-GUI is a framework for the creation of graphical interfaces for configuring
За да конфигурирам GUI-то използвах това упътване:
http://www.asteriskguru.com/tutorials/asterisk_gui.html
След като настроих Asterisk-a по мой вкус, вече имам няколко soft phone-a и двата SPA 941 свързани и работещи.
Това което ми липсваше на този момент е връзка със останалия свят.
Много добра тема по въпроса може да намерите тук:
http://www.kaldata.com/forums/index.php?showtopic=6681&st=0
ето и няколко упътвания:
http://akrozia.org/?tag=asterisk
http://ygeorgiev.net/archives/56
http://forum.spectrumnet.bg/showthread.php?t=2573
Накрая се насочих към BGOpen.
Регистрирах се, захраних сметката си с известна сума. И вече имам телефонен номер ала +3592490ХХХХ.
Прегледах няколко интересни статии по въпроса:
http://ygeorgiev.net/archives/56
http://forum.spectrumnet.bg/showthread.php?t=2573
Сега е необходимо да научим Asterisk-a за този номер, и как да го ползва.
Първо отиваме в Trunks, VOIP Trunks и избираме + New SIP/IAX Trunk
Избираме тип-а – SIP
Така и не успях да го подкарам с IAX, ако някой го е подкарал и има впечатления нека ги сподели.
За Hostname: sip.bgopen.net
Username / Password – каквито сте избрали при регистрация в bgopen.
Codecs: според FAQ-a на BGOpen
Можем да ползваме G.729, G.723.1, GSM, iLBC (поне един от изброените)
За CallerID и Enable Remote MWI не съм сигурен, за това ги оставих празни.
След това отидох в Outgoing Calling Rule, и създадох нов като Pattern: _9. – тоест всички номера които имат 9 от пред се насочват към създадения преди малко Trunk.
Избрах името което съм дал на Trunk-a в полето Use Trunk
Strip – 1 тоест да маха 9-тката при набиране на вън.
Редактирах DialPlan-a си да включва и Outgoing Calling Rule-a
Сега вече мога да набирам не само слушалките директно свързани към Asterisk, но и каквито ми хрумне навън. Единствено трябва да сложа една 9-ка пред номера.
Дойде време да могат и мен да ме търсят по новия ми номер +3592490ХХХХ.
За целта отидох в Incoming Calling Rules, създадох ново, като избрах
Trunk – който създадох по – горе
Time Interval – None
Pattern: _X. – да препраща всички номера към
Destination: Тук мога да избера номер или voice mail на някоя от слушалките. За тестове избрах един номер, но аз не искам това, а Voice Menus за да си създам IVR.
Вече имате входящи и изходящи обаждания и гласова поща.
Да нагласим Voice Menus
Създадох ново, избрах му name и extension
Тук трябва да се добавят Actions, действия които ще се извършват едно след друго.
Ето и моите:
Answer the call – все пак трябва да вдигнем на човека
Set(TIMEOUT(digit)=5) – колко време чакаме преди да спрем да чакаме за бутон
Set(TIMEOUT(response)=20) – колко време да чакаме за натискане на бутон
Play record/X & Listen for KeyPress events – пускаме на човека записано съобщение с инструкции коя цифра с кого ще го свърже, ако бъде натисната
Play record/Silance & Listen for KeyPress events – наложи се да направя втори запис, със тишина, за да дам време на обаждащия се да натисне някоя цифра, иначе веднага след приключването на предишния запис затваряше линията.
Hangup call – затваряме линията ако не е натисната цифра.
Тук имах див проблем с extension-a. В option има секция Extensions preferences в която за Voice Menus са заделени номера от 7000 до 7500. Проблема ми беше че ако избера в този диапазон не можех да набера номера, а ако се опитам да избера извън него не ми позволява. За това се наложи да го разширя до 8000 и сработи.
След това в Incoming Calling Rule само Destination полето се насочва към Voice Menu-то Extension-a който създадох.
Вече ако някой се обади на номера ми +3592490ХХХХ ще го посрещне записано съобщение което ще го информира кой номер да натисне за да се свърже с мен. Ако ме няма ще бъде насочен към гласовата ми поща, за да остави съобщение.
Какво следва
Когато намеря време и пари за това ми се иска да свържа и POTS към Asterisk-a. Тоест и
стария ми домашен телефонен номер от БТК да влезе в играта.
За целта ще ми е необходимо някакво устройство което да направи връзката.
Това устройство много ми харесва: CISCO SPA3102 2-Port Router with 1 FXO + 1 FXS
http://www.voip-info.org/wiki/view/Linksys-Cisco+3102
То може да свърши тази работа за мен.
Ето малко локална информация за него:
http://hardwarebg.com/forum/showthread.php?p=1780708
http://www.comelsoft.com/product.php?mf=cisco&lang=bul
Създаване на Phone Book, тоест входящите обаждания да се идентифицират по Caller ID, и да се изписва Име и номер на търсещия, не само номера му.
Последното нещо което трябва да пробва е да получавам факсове, по принцип услугата е активиране по подразбиране от bgopen, но никога да сега не съм я ползвал и незнам точно как работи. Както и ми е интересно какви възможности за изпращане на факсове имам.
Надявам се темата да ви е била полезна.